Healthcare startups and software companies that want to enter the healthcare industry have to remember HIPAA compliance regulations. Especially if the application is targeted at users of the USA. HIPAA rules are enforced by law and those companies that fail to comply with requirements for security and privacy of data can be fined with tremendous penalties.
HIPAA, or the Health Insurance Portability and Accountability Act, made a big deal about how organizations treat private patient info. Whether you're upgrading an existing healthcare app or dreaming up a new one, you've got to play by HIPAA's rules. Fortunately, there is plenty of open-source information, training, webinars, and guides from the Compliancy Group, the Department of Health and Human Services that govern the regulations globally.
In this guide, we'll break down what HIPAA compliance is all about and give you the lowdown on building apps that keep health info safe. Whether you're a tech whiz or just starting out, we've got your back: our tips and tricks, straight from our experience of HIPAA compliance in software development at Inoxoft, will guide you through the whole process.
- Why is Medical Data Hunted?
- What is HIPAA Compliance?
- When was HIPAA implemented?
- To whom does the HIPAA apply?
- What Does HIPAA Mean for Software Companies?
- When Do You Become HIPAA-Compliant?
- What Solution Can Be Defined as HIPAA Compliant?
- What is the HIPAA IT Compliance Checklist in IT?
- HIPAA privacy rule
- HIPAA security rule
- The HIPAA breach notification rule
- The HIPAA omnibus rule
- The HIPAA enforcement rule
- Technical safeguards
- Authorization and password requirements
- Audit and activity logs
- Automatic log-outs and session expired
- Third-party tools
- Email encryption
- Data backups
- How to Choose the Right HIPAA Compliance Software for Your Business?
- Step #1: Identify your pain points
- Step #2: Check vendor credentials and look for references
- Step #3: Check the price of the service
- Step #4: Request a free trial
- Is Azure HIPAA compliant?
- Consider Inoxoft your trusted partner
Why is Medical Data Hunted?
Electronic medical records are targeted more often by hackers than credit cards and banking systems. Hackers’ malicious actions are usually planned, intentional, and “jewelry” work. In an attempt to steal ePHI, they use a combination of technical and social engineering methods, managing to crack systems within hours. And, they crack user-generated passwords within minutes.
Why do hackers deliberately hunt for medical records? Electronically protected health information is deeply personal, confidential, and unique, which, often, cannot be restored. It is used for lucrative hacker schemes, blackmailing, and demanding ransoms.
Hackers can obtain loans, get free medical insurance, and request treatment or drugs on behalf of patients, using their stolen identities. Fraudsters can receive refunds for treatment that has never been provided, make protected health information public, cause information wars, and serve as spies causing international political issues. Medical systems that are less protected than banking systems can also contain payment card information. That’s one more tidbit for crackers.
What is HIPAA Compliance?
The acronym for HIPAA is the Health Insurance Portability and Accountability Act. It governs two critical branches — the HIPAA Privacy and Security Rules for the use and disclosure of Protected Health Information or just PHI. Pictures of scanned organs, medical voice records, analysis tests, diagnoses, addresses, geolocation of patients are defined as the information that should be thoroughly protected. So not to allow fraudulent actions and unpredictable consequences of disclosing data to the public.
When was HIPAA implemented?
HIPAA rules were originally enacted in 1996 in the USA. They were signed under the key objective of protecting waste, fraud, and abuse of protected health information. At the same time modernizing healthcare services.
Interestingly, the evolution of electronic records started in 1972, when the first electronic medical system was developed. Although being very expensive, such systems offered vast opportunities for governments and hospitals.
In the 1990s with the emergence of the Internet, more affordable prices for the first PCs, popularity and demand for healthcare systems increased, though they certainly were much more simple than today. So, dynamic and growing technologies in Healthcare caused a need for creating a plan (which is HIPAA itself) on how to moderate risks connected with personal health information.
To whom does the HIPAA apply?
The Act defines a category of Covered Entities and Business Associates that must apply to the standards. Business Associates can be a law office, software company or IT consultant, accounting services, and companies that build hardware medical devices. And those, who cooperate with healthcare providers and have direct access to ePHI. These are also companies that provide data storage solutions and all their subcontractors.
Covered entities include healthcare providers which are doctors, dentists, clinics, pharmacies, nursing homes, and more on the list if they have access to electronic medical data. The second category is Health Plans, which are health insurance companies, government medical programs, or health maintenance organizations (HMOs). The last category includes healthcare clearinghouses.
What Does HIPAA Mean for Software Companies?
HIPAA compliant software requirements for software providers take effect if a software company deals with a solution that reveals, collects, and processes personal identifiers of patients. To understand what is PHI exactly there are 18 defined features of PHI. If any application uses at least one of the indicated features, it automatically should apply to HIPAA IT requirements.
Usually, developing healthcare applications is executed on behalf of a covered entity that provides services in accordance with HIPAA. And, also, knows how to cooperate with developers to make the solution fully compliant. In general, software engineers have to help eliminate the risks associated with the privacy and security of electronically protected health information. They should ensure network compliance with appropriate transmitting, messaging, and data storage solutions.
An example of experience we had in the Healthcare industry was cooperation with an Israel emotion-recognition startup Beyond Verbal. For the application collecting and analyzing patients’ voice records, building an elaborate business logic was a key to success. The developing process was based on their sharing of practical knowledge of HIPAA rules with us and our technical expertise on how to implement it properly, on time, and in a cost-effective manner.
However, how and when software companies should regard the software HIPAA compliance checklist is circumstance-framed. Ambiguity around HIPAA requirements for software puts a lot of companies in a deadlock. That’s why there was an initiative to discuss cases when software developers, especially those, who independently create healthcare solutions, can ask their questions and clarify with experts obscure situations to avoid penalties.
When Do You Become HIPAA-Compliant?
When does your application become HIPAA compliant and when it does not? When do you become a BA (Business Associate) of a medical provider and when not?
Imagine 100 patients installing your mobile application and inputting the information regarding their emotions, diet balance and the number of heartbeats, and more. The application was made at the request of some clinic – your client. Additionally, they decided to connect the application with a local EHR system and all the data would automatically be transferred and incorporated into the EHR. As a result, patients receive consultations from specialists and use messaging tools to share files and communicate with doctors.
You would have to implement cloud solutions, and ensure secure authentication and configuration of the system having direct access to ePHI. In such a case, you as a healthcare developer become a business partner of a medical provider. By signing a contract with your covered entity, you are responsible for creating all conditions of safe sharing, processing, and storing the ePHI.
What Solution Can Be Defined as HIPAA Compliant?
The development and usage of devices and applications that contain ePHI should comply with physical, technical, and administrative safeguards. From the side of software development companies, applications for medical institutions should thoroughly cover HIPAA compliance and be checked through the HIPAA compliance checklist Summarizing the technology checklist items, the solution containing ePHI should:
- allow access only for authorized users
- be tested for secure sending attachments and images that contain PHI, as well as secure messaging
- have encrypted data that can not be legible in case of cyberattacks
- integrate with secure data storage
What is the HIPAA IT Compliance Checklist in IT?
Here’s the HIPAA compliance checklist for software development you should know about:
HIPAA privacy rule
Privacy rules mean that patients have the right to examine and watch their information on the condition that access to data is authorized. From 2013, the HIPAA privacy rule applies to business associates of covered entities. From the side of business structures, it is important to provide all necessary tools and possibilities to maintain the integrity of ePHI. And, to create procedures of how it would be tracked if any alterations happen. The Privacy rule that can be found at the website of Health Information Privacy also means that patients have to receive electronic copies of their personal health information by request within 30 days.
HIPAA security rule
The Security Rules govern how ePHI should be appropriately used, kept, and transmitted. And, what are the ways to ensure the protection, confidentiality, and security of information technology data? Because reasons for violations of security can be different, special safeguards are serving as guides to understanding all levels of the security management process:
- Administrative safeguards
- Physical safeguards
- Technical safeguards
HIPAA Privacy rules refer to PHI integrity and correct on-time disclosure to legal patients. The HIPAA Security Rule refers to the protection of electronic PHI that is stored and transmitted by digital devices and across networks. Besides, you’ll meet Addressable safeguards that presuppose a certain amount of flexibility for covered entities. And, business associates, who can develop alternative ways to cover the safeguard rules on condition every alternative is properly documented.
Physical safeguards focus on controlling physical access to data, and monitoring location, and devices. Workplaces have some restrictions in use and have to guarantee the safe surroundings of devices on which sensitive data is kept. Physical and technical safeguards regulate the use of ePHI on hardware and software and if any device is moved, it should be inventoried and data should be copied.
The HIPAA breach notification rule
Covered entities must notify the Department of Health and Human Services of breaches that affect the protected health information of more than 500 people. As an example, cases of breaches of Australian databases were immediately disclosed to the media, and the necessary procedure was conducted to inform each patient of the emergency. Among people whose information was stolen were officials and people holding government positions. Presenting such notification needs evaluation of the system by software engineers. And, their help to understand how and when unauthorized access happened, whether data was acquired or viewed, and what risk mitigation measures were.
The HIPAA omnibus rule
The rule amends and updates regulations, establishing a better understanding of the terms Business Associates, Workforce, and Covered entities. According to the Omnibus Rule, covered entities have to sign contracts before cooperating with BA.
If you are sharing PHI with a covered entity, then, as a developer, you are required to sign a Business Associate Agreement that validates permissible uses of PHI. In all other cases, when you don’t have access to ePHI, you are not BA. Old signed agreements are to be renewed. Updated Privacy Policies, fundraising, research, and marketing of ePHI, as well as training staff, can be done according to Omnibus regulations.
The HIPAA enforcement rule
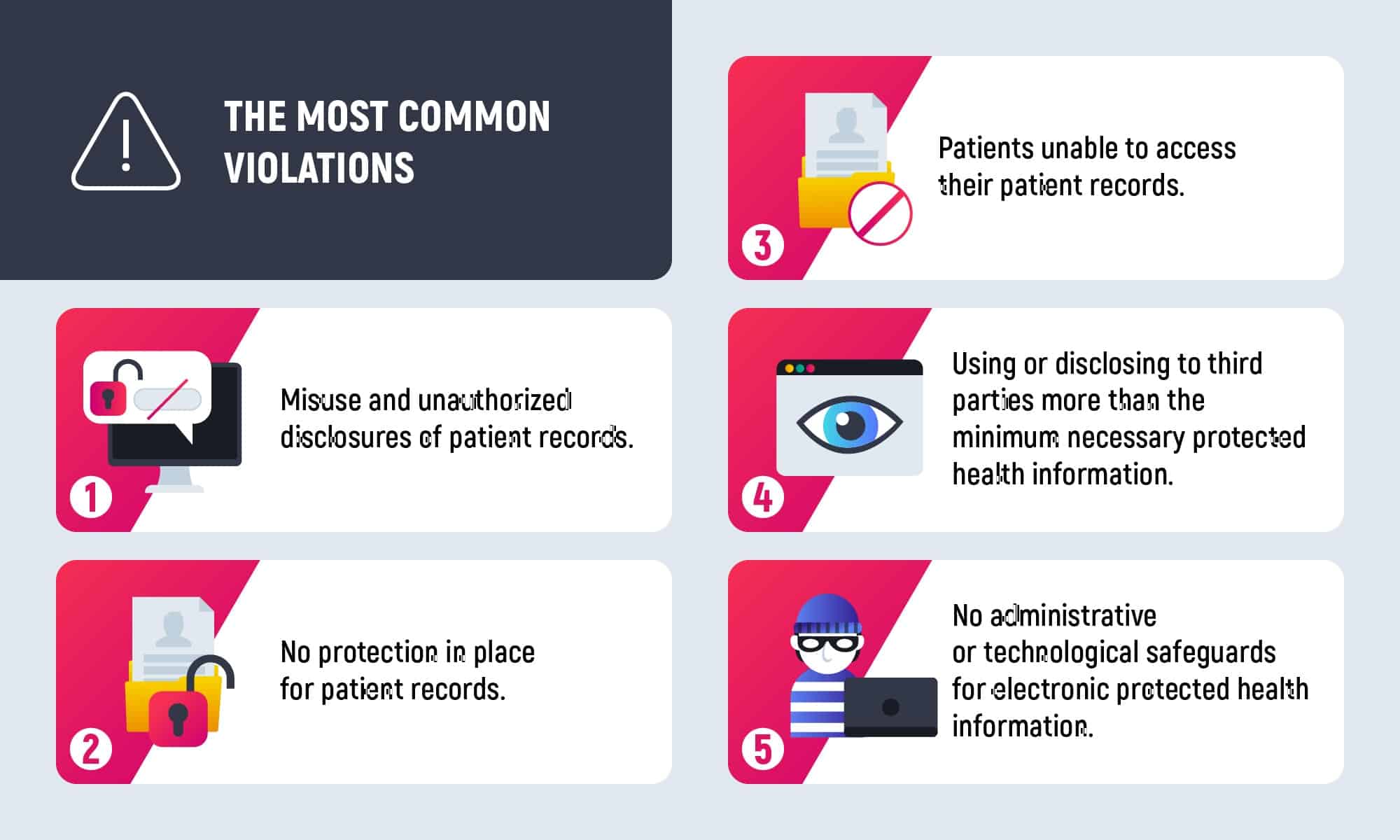
The rule governs the penalties imposed for responsible sides, who failed to comply with HIPAA regulations. And, dictates procedures for the investigation of the breaches. The number of records at risk, category, and level of ignorance is measured for defining penalties. The maximum fine can reach $1.5 million. The minimum one, which is a violation based on ignorance of the responsible side, starts at $100. By HIPAA journal, the most common violations are the next:
Technical safeguards
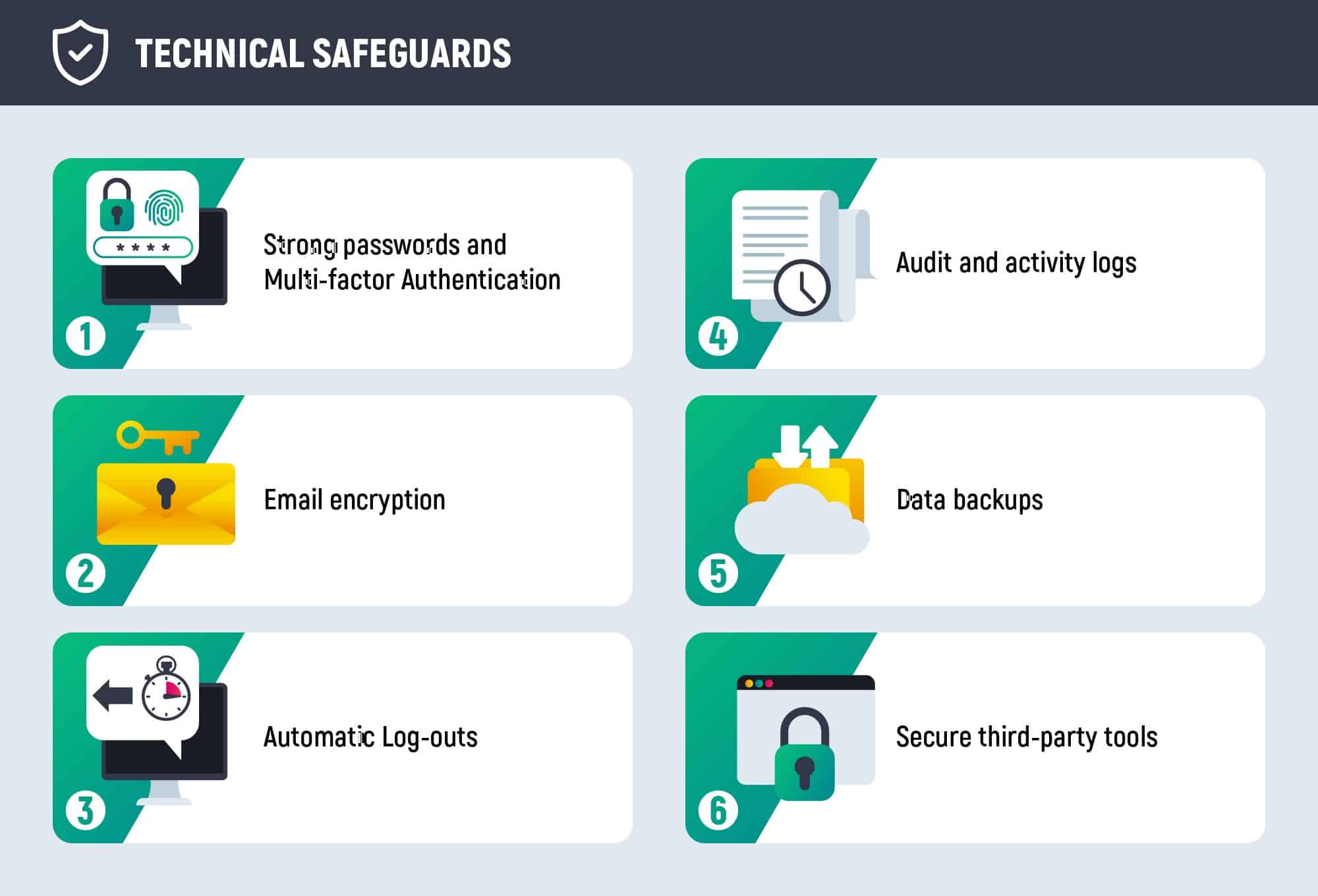
Returning to the Security Rule, in terms of its technical safeguard software developers together with healthcare institutions should develop perfect business logic for the software so that it complies with regulations. Technical safeguards presuppose that electronic data that travels across servers and networks, should be protected and access-authorized. This safeguard can be carried out on the condition ePHI is encrypted according to NIST standards.
Authorization and password requirements
HIPAA Password requirements are addressable safeguards. It means they should be necessarily implemented, but there are alternatives allowed only if all of them are documented. That’s how HIPAA states the definition
implement one or more alternative security measures to accomplish the same purpose.
HIPAA compliance software requirements recommendations on passwords:
- The best way is to implement two-way authentication. In addition to logging in to the app and receiving SMS or push notifications, a person accessing PHI should use credentials to confirm identity.
- Password should be strong with uppercase letters, numbers, and special characters.
- Password management tools that save a password in an encrypted format are less likely to be hacked.
The HIPAA requirements also demand to establishment policies to control and govern data disclosure in emergencies.
Audit and activity logs
It is essential to know, who has altered the data, as well as to track the geolocation of employees. In terms of access management, the effective way to implement it is by monitoring log-on activities and restricting access when employees change job positions. Users are often provided with the possibility of a VPN (Virtual Private Network) connection. And, automatic downloads are not allowed.
The downloadable HIPAA compliance checklist for IT puts 6 required annual Audits as the first question to understand whether your organization is HIPAA compliant. Audit Controls in terms of network management helps to monitor user access on a network and provide administrators with notifications if suspicious activity occurs. Audit controls help to register each attempt to access the patient data and quickly detect inside breaches.
Automatic log-outs and session expired
Remember to facilitate automatic log-outs after a defined period. Imagine some personnel working with a solution and presuming they may leave it unattended because of external conditions. To make sure, data is not disclosed or seen by anybody else, the system will ask to relog due to the session expired. Returning to our experience with Beyond Verbal, Inoxoft engineers developed a system that automatically deletes an installed application after necessary surveys were filled by patients.
Third-party tools
There are tools like BitLocker for Windows or FileVault for Mac OS that help to encrypt hard drives containing PHI. Software solutions like TrueVault and Aptible help safely store protected data. The security management process includes the usage of data loss prevention software and IP protection. Make sure HTTPS, which encrypts data with SSL/TLS and transforms PHI into unreadable for hackers’ lines of information, is implemented whenever login and password forms are filled and sent.
Cybersecurity Policies also concern data visibility control to track how patient data is used, how much time personnel spend accessing databases on clouds, networks, and endpoints. The developed NIST Cybersecurity Framework will help you to prevent data breaches. And, also, detect and respond to attacks in a HIPAA-compliant manner when attacks do occur.
Email encryption
Depending on how email is being used, the rules differ. When sending an email internally, using an organization’s internal network, it is not necessary to use encryption. However, when sending external emails, that pass through a third-party server, encryption is recommended. Encryption is the most effective way to secure PHI as it scrambles data, making it unreadable without a decryption key.
Data encryption is an effective way to minimize risks during losses, and theft. Or, when ePHI is moving across open networks. Encrypted data is ciphertext, which is a plain text of encryption, unreadable for machines and people without a cipher, an algorithm that converts step-by-step information into code. Data encryption is also possible on networks not allowing hackers to intrude.
Data backups
The common solution for restoring patient data is backups. Administrative safeguards demand healthcare organizations to assess possible risks and attacks against ePHI. And, regularly conduct simulation attacks to understand whether a contingency plan works well enough to restore lost data.
How to Choose the Right HIPAA Compliance Software for Your Business?
Choosing the right HIPAA compliance software for your business is crucial for safeguarding sensitive healthcare information. Here are some steps to help you make an informed decision:
Step #1: Identify your pain points
Understand your organization’s specific needs and challenges related to HIPAA compliance. Identify the areas where you need assistance, such as data security, access controls, audit trails, and risk assessments.
Step #2: Check vendor credentials and look for references
Ensure that the software provider has a good reputation and a history of dealing with healthcare organizations. Look for certifications such as HITECH or HITRUST. Check for references from other healthcare entities that have used the software successfully.
Step #3: Check the price of the service
Compare the pricing of different HIPAA compliance software solutions. Be sure to consider your budget constraints and evaluate whether the software offers value for the cost. Some software may have a one-time licensing fee, while others may have a subscription model.
Step #4: Request a free trial
Reputable HIPAA compliance software providers offer free trials. Requesting a trial allows you to test the software’s features and functionality within your organization’s environment. Pay attention to user-friendliness, integration capabilities, and overall usability during the trial period.
Is Azure HIPAA compliant?
HIPAA compliance for software development does not restrict software developers from using particular cloud services for storing ePHI. However, HIPAA Journal explains in what way covered entities and developers can rely on beneficial cloud services. And, whether all of the cloud providers are HIPAA compliant.
Microsoft cloud services are used widely, so the arising question is whether Azure is HIPAA compliant. Would not there be any violations on the side of covered entities using Azure for PHI? The truth is, HIPAA software requirements compliance is achieved under 2 conditions:
- It is the responsibility of covered entities to ensure that the server provider meets the necessary safeguards to cover HIPAA Security and Privacy rules.
- Before any PHI can be stored in the cloud, covered entities have to sign a Business Associate agreement with service providers. Even if cloud providers do not access directly customer information, a BAA is required.
Azure supports HIPAA compliance regulations and provides secure hosting for data, necessary encryption, VPN connections, possibilities for great access controls, and setting permissions, who can access the data and monitor accesses and alterations with data.
In general, Azure does meet HIPAA compliance, however covered entities have to understand and ensure that all safeguards are covered and staff is appropriately trained on the use of the service. To note, Microsoft teams will not be charged and do not accept responsibility for violations caused by the inappropriate application of their services.
Consider Inoxoft your trusted partner
Inoxoft is a healthcare software development company. We engage in custom mhealth app development and are the top telemedicine app development company. Building cutting-edge solutions for startups and other clients requires full comprehension of the process, tracking of market trends, and complying with certain laws. Thus, in building HIPAA-compliant software we take into account every nuance there is. Our certified engineers are capable of meeting HIPAA technology requirements and deploying any CRM in the healthcare industry.
By so far, we have implemented numerous projects for our clients in healthcare. Some of them were mentioned in the article. Each of these projects was carried out according to the HIPAA IT compliance checklist.
Contact us to receive the best healthcare app on the market! Apply for DevOps outsourcing to build the world’s finest software solutions with Inoxoft. We are the best among vendors and the best development technology partner to build your HIPAA medical software. Get in touch with us today and reap benefits tomorrow!
Frequently Asked Questions
Is HIPAA compliance software the same for covered entities and business associates?
The core principles of HIPAA compliance apply to both covered entities and business associates, but the specific requirements and responsibilities may vary between the two.
Covered Entities:
- Covered entities, as defined by HIPAA, include healthcare providers, health plans, and healthcare clearinghouses. These organizations directly handle patient health information and are subject to the full scope of HIPAA regulations.
- Covered entities are responsible for implementing comprehensive security measures to protect the confidentiality, integrity, and availability of patient information. They must also comply with the Privacy Rule, Security Rule, and Breach Notification Rule.
Business Associates:
- Business associates are entities that perform certain functions or services on behalf of covered entities and involve the use or disclosure of protected health information (PHI). Business associates can include IT vendors, billing companies, consultants, and others.
- While business associates are not directly covered by all aspects of HIPAA, they are still obligated to comply with certain requirements. They are typically required to sign a Business Associate Agreement (BAA) with covered entities, which outlines their responsibilities for safeguarding PHI and complying with certain aspects of the HIPAA regulations.
Why is it important that a software vendor understand HIPAA rules?
It is crucial for a software vendor to understand HIPAA rules especially if their software is used by healthcare organizations or entities dealing with protected health information (PHI). Here are key reasons why HIPAA understanding is important for software vendors:
Legal Compliance:
Healthcare organizations and their business associates are legally obligated to comply with HIPAA regulations. If a software vendor's product is used to handle PHI, it must align with HIPAA requirements. Failure to comply can result in legal consequences, including fines and penalties.
Customer Trust:
Healthcare organizations and professionals rely on software to manage and process sensitive patient data. If a software vendor understands and complies with HIPAA rules, it builds trust with customers. This trust is essential for maintaining long-term relationships and ensuring that customers feel confident in the security of their data.
Avoiding Data Breaches and Penalties:
Non-compliance with HIPAA can lead to data breaches, which can have serious consequences for both the software vendor and their customers. Understanding HIPAA rules helps the vendor implement robust security measures, reducing the risk of data breaches and potential penalties associated with non-compliance.
Business Associate Agreements (BAAs):
Healthcare organizations often require their vendors to sign Business Associate Agreements (BAAs). A BAA is a legal document that outlines the responsibilities of the vendor in safeguarding PHI. To comply with HIPAA, vendors must understand the terms and requirements specified in these agreements.
Security Measures Implementation:
HIPAA mandates specific security measures to protect PHI, including encryption, access controls, audit trails, and risk assessments. A software vendor with a solid understanding of HIPAA rules can incorporate these security features into their product, helping customers meet compliance requirements.
Risk Management:
HIPAA requires entities to conduct regular risk assessments to identify and mitigate potential vulnerabilities. A software vendor that understands HIPAA can assist customers in managing risks associated with the use of their software, contributing to overall compliance efforts.
Staying Informed About Changes:
HIPAA regulations may evolve over time. A software vendor must stay informed about any changes to the rules and update their software accordingly. This ensures that their product remains compliant with the latest standards and best practices.
Educating Customers:
Software vendors that understand HIPAA rules can educate their customers about compliance requirements and how to use the software in a manner that aligns with these regulations. This education is valuable for healthcare organizations seeking to implement and maintain HIPAA compliance.
.
What are HIPAA software requirements?
HIPAA requirements for HIPAA software providers take effect if a software company deals with a solution that reveals, collects, and processes personal identifiers of patients. To understand what is PHI exactly there are 18 defined features of PHI. If any application uses at least one of the indicated features, it automatically should apply to HIPAA IT requirements.