The world is constantly evolving and offering people a lot of opportunities. Digitalization had an impact on basically every industry out there. Big Data can store loads of information and give people access to any source they are interested in. Cloud computing has already influenced education, software development, and real estate, and the banking sphere is no exception. Traditional ways of storing information are not so relevant nowadays, as their technology has gotten old and has less to offer. That’s why tons of banks are changing their perspective and trying to keep up with the latest technology updates. Cloud computing, for sure, is one of them.
With the help of cloud computing in banking it becomes easier to handle and analyze any kind of data. Moreover, it is much safer, as the banks need to have a sense of security. One of the pros of cloud computing in financial services is the ability to save money for the company. It’s quite clear that using cloud-based services heavily increases the efficiency of a company’s work, as it is always accessible and doesn’t require additional tools.
The article will tell you everything you need to know about cloud computing in banking industry, why it is important nowadays and what are the main reasons for using it. It will also give you some pieces of advice how to properly utilize cloud-based services to improve the quality of your work.
- What is Cloud Computing?
- The Role of Cloud Computing in Banking Industry
- What Are the Main Reasons for Using Cloud Computing for Banking Services?
- Lower risks
- Productivity
- Cost savings
- Better Security
- Compliance with Regulations
- Advanced Customer Relationship Management (CRM)
- Easy Scalability
- Improved Customer Experience
- Green IT
- Greater Operational Efficiency
- Choosing the Best Cloud Computing Model for Financial Services
- Cloud Service Models
- Cloud Deployment Models
- Cloud Operating Models
- Cloud Computing Challenges in the Banking Industry
- Data Privacy and Security
- Regulatory Compliance
- Lack of Control
- Risk Management in Cloud Banking Systems
- Regulatory Compliance
- Reputational Risk
- Operational Risk
- Strategic Risks
- Final Thoughts
- Consider Inoxoft Your Trusted Partner
What is Cloud Computing?
Cloud computing involves providing servers, storage, databases, networks, and software over the Internet. Instead of owning and managing physical hardware and software, companies access these resources on a pay-per-use basis.
You can scale cloud resources up or down quickly to meet changing workloads and requirements. Billing is based on the actual use of cloud resources, allowing you to precisely control and optimize costs.
The Role of Cloud Computing in Banking Industry
It is widely known that the banking industry requires precision and calculation, which can be time-consuming. Big Data is truly irreplaceable in this sphere. Automated processes increase efficiency and performance, that’s why they are so essential in the industry. However, this is not the only reason why the importance of cloud computing is hard to overestimate.
First of all, cloud computing for financial services allows banks to maintain a direct connection with the customers. It doesn’t matter what their location is, with the help of cloud-based services you can easily deal with a lot of challenging issues. Traditional storage does not always allow keeping big amounts of data, so they can be impractical and cause a lot of difficulties. At the same time, there is no such situation with the cloud. You can organize and manage your services without any problem because executing operations using cloud computing are really efficient.
The bank can also pay more attention to the user, as one of the main advantages of cloud computing in banking is reliability. Cloud-based services organize all the processes and leave the customer with a feeling of security. Also, digitalization of the banking process is also really beneficial for the whole industry.
All in all, the impact of cloud computing in banking is great and is definitely a moving factor for the industry’s development in today’s world.
What Are the Main Reasons for Using Cloud Computing for Banking Services?
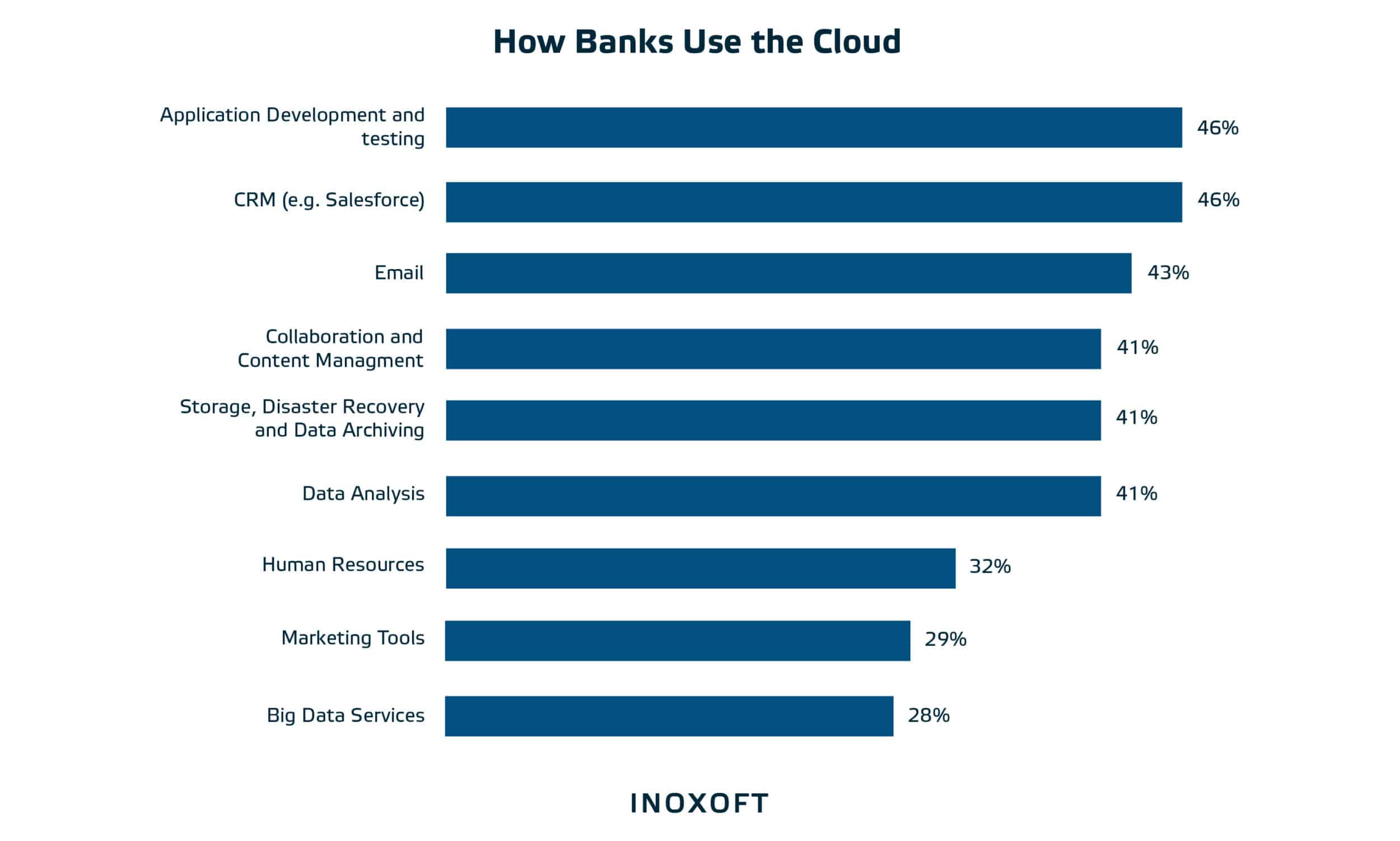
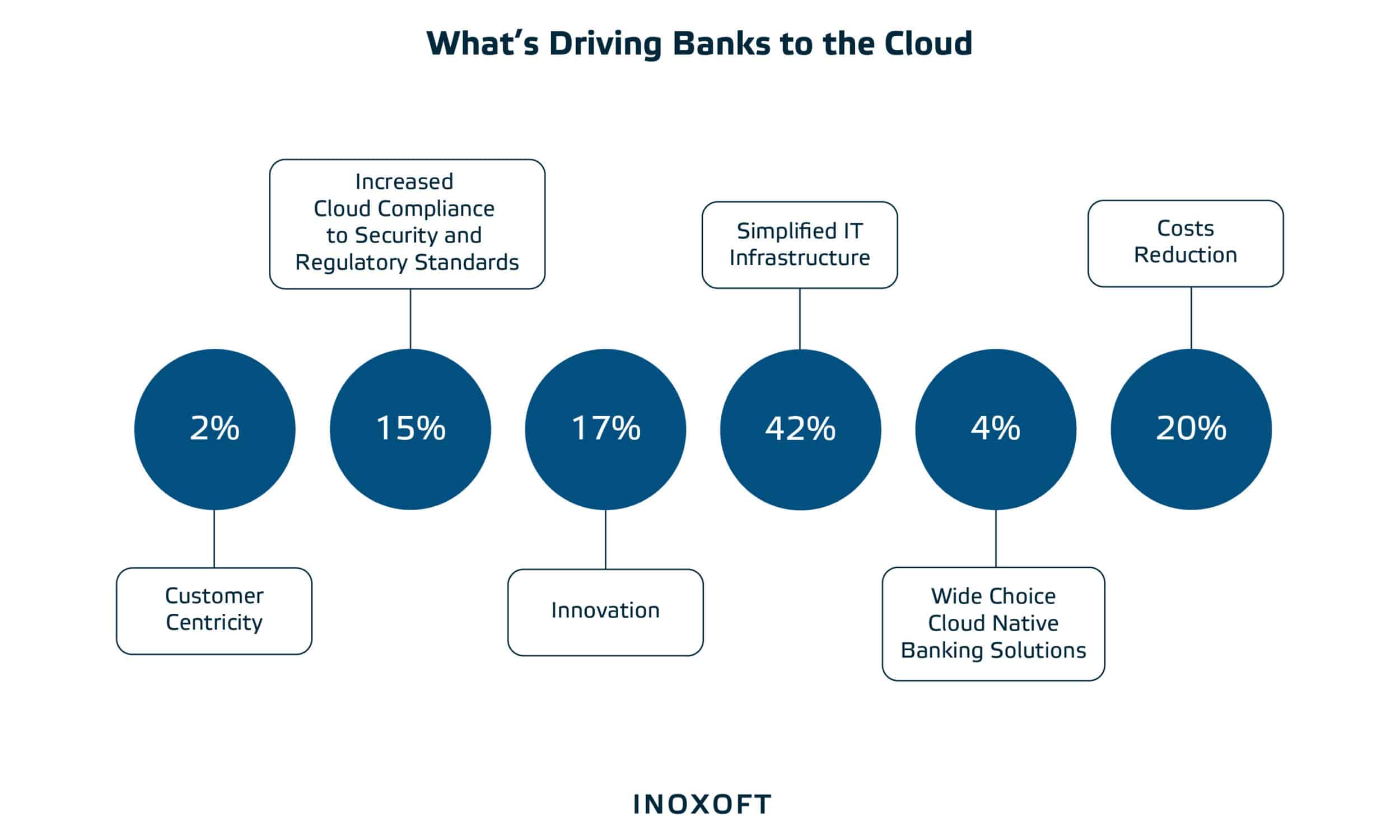
Cloud adoption in banking services is a great way to modernize processes, save time and handle all the necessary data. With the help of cloud services, you can achieve your goals faster and more efficiently. Here are key reasons why banks are cloud computing, given by The British Bankers’ Association.
Lower risks
No doubt, safety is really important for every company. Traditional technologies used to be reliable some time ago, or so they seemed. Nowadays there are a lot of risks which are associated with traditional ways of dealing with banking issues. Cloud-based banks can feel more secure, as they are more resilient to different damaging factors. You can easily prevent financial crimes and avoid money laundering.
Productivity
Cloud computing for banks is a great way to boost their productivity and therefore, open the way for innovations. Unlimited access to one source always helps generate new ideas and makes it easier. Moreover, new technologies are easily paired with convenience for customers and bankers. Without innovations, there is no growth for the company, and in today’s world, that’s a pretty reasonable factor.
Cost savings
It goes without saying, that the more advanced the cloud is, the more possibilities it has to offer to a company. Improvements in the business sphere provide cost benefits, as requirements for traditional technologies are no longer relevant. It helps bankers to prioritize things and decide which project is worth investing in, and which is not.
Better Security
Cloud computing for banking offers advanced security measures, such as encryption, multi-factor authentication, access control, backup, and constant monitoring. Providers invest heavily in cybersecurity, often beyond what individual banks can handle. This reduces the risk of data leakage and cyber-attacks. Also, you can ensure data availability in the case of unforeseen events.
Compliance with Regulations
Want to facilitate automated compliance monitoring and reporting? Cloud service providers often have global certifications and compliance standards that banks can use to meet industry requirements. Audit logs and data retention policies are easier to apply and manage in the cloud. Data encryption and secure access controls help banks comply with data protection laws such as GDPR or HIPAA.
Advanced Customer Relationship Management (CRM)
Centralize customer data to give employees a complete overview of client interactions and preferences. You can use the stored data for analytics and machine learning to gain information about user behavior and adapt your services. Also, you free up employees’ time for more complex issues by automating routine tasks. All of this improves customer interaction and satisfaction.
Easy Scalability
Cloud infrastructure allows banks to easily scale their computing resources based on demand. This way, you can handle peak loads without investing in expensive on-premises equipment. It will also be useful for quickly deploying new services and applications or expanding your operations worldwide with minimal infrastructure setup. At the same time, you reconcile costs with actual use.
Improved Customer Experience
Give your customers convenient access to their accounts and financial services through web and mobile applications. With cloud computing in finance, they can update account balances, make transactions, and use other self-service features in real time. Cloud-based AI and chatbots provide instant customer support by responding to queries and resolving issues quickly.
Green IT
Cloud computing is often more energy-efficient and has a lower carbon footprint than on-premises data centers. This is due to the optimized use of resources. The shared cloud infrastructure model minimizes hardware costs and reduces the need for frequent hardware upgrades. Banks can also achieve significant energy savings, contributing to environmental sustainability.
Greater Operational Efficiency
Automate routine tasks like software updates, backups, and system monitoring. It reduces manual work and minimizes errors. You can forget about extensive local maintenance and equipment management with the cloud. Disaster recovery and business continuity capabilities in the cloud ensure uninterrupted operations. At the same time, collaboration and document management tools increase workflow efficiency.
As we can see, the impact of cloud computing for banking industry is really significant. Using cloud services is good for cost management and coming up with new ideas. Convenience is also a deciding factor, as the companies definitely benefit from automatized processes and guaranteed safety. If you are interested in improving your business, catching up with new technologies is a must.
Choosing the Best Cloud Computing Model for Financial Services
Despite various cloud banking benefits, selecting an appropriate model is critical in successful cloud development and integration.
Cloud Service Models
Cloud service models define the level of control and responsibility of cloud providers and users in managing various aspects of computing resources and services.
- Infrastructure as a Service (IaaS). This includes virtualized computing resources, such as virtual machines (VMs), storage, and networking. Users have significant control over the operating systems, applications, and data on the provided infrastructure. IaaS is typically used for development and testing environments, hosting websites, and running custom software.
- Platform as a Service (PaaS). PaaS includes the infrastructure and the tools and services needed to develop, deploy, and manage applications. Cloud users can focus on writing code and deploying their applications without worrying about the underlying infrastructure. This allows you to optimize application development and reduce time to market.
- Software as a Service (SaaS). SaaS provides full-featured software applications on a subscription basis. Users have little control over the underlying infrastructure, operating systems, or application code. The most famous SaaS solutions include Gmail, Microsoft 365, Salesforce, Slack, etc.
Cloud Deployment Models
Cloud deployment models define how cloud computing resources and services are physically provided and organized.
- Public cloud. In this model, cloud infrastructure and services are owned and operated by third-party providers and are available to the general public. These cloud resources are usually hosted in data centers in different geographical locations. Public clouds offer scalability, cost-effectiveness, and availability.
- Private cloud. A private cloud is an environment dedicated exclusively to one organization. It can be hosted locally in a company’s own data centers or provided by a third-party cloud service vendor. Private clouds offer better control, security, and customization options.
- Hybrid cloud. A hybrid cloud combines elements of a public cloud and a private cloud, sharing data and applications between them. Companies can leverage the scalability and cost-effectiveness of the public cloud for non-sensitive workloads while keeping sensitive data and critical applications in the private cloud.
Cloud Operating Models
Cloud operating models offer organizations different approaches to managing their IT and cloud-related operations.
- Virtual captives. A virtual captive is an organization’s subsidiary or special offshore unit that operates in a foreign country to benefit from cost-effective labor markets. This provides direct control over processes, enables cost savings, and provides access to a global talent pool. However, companies must invest significantly in infrastructure, legal requirements, and operational overheads.
- Staff augmentation. This model assumes an increase in personnel by hiring additional IT staff from external suppliers. This way, companies can easily scale teams, access specialized skills, and save on overhead costs. However, integrating external personnel into the existing team and ensuring effective collaboration can be challenging.
- Outsourcing vendors. These external service providers undertake certain IT functions or services, from infrastructure management to application development and support. Companies can save money, flexibly adapt to market changes, and focus on core competencies. However, this means a partial loss of control over the outsourced functions.
Cloud Computing Challenges in the Banking Industry
What challenges should you be ready for when using cloud computing in banking sector? Let’s consider the most important ones.
Data Privacy and Security
Cloud for banking involves shared infrastructure using the same servers and resources. This could potentially expose banks to security vulnerabilities if proper isolation and measures are not implemented. Improperly configured encryption settings or key management can also lead to vulnerabilities.
Regulatory Compliance
Banks must ensure that vendors meet industry compliance standards. This includes evaluating the supplier’s certification, security controls, and ability to assist with compliance efforts. In addition, some countries require certain financial data to be stored within their borders, which is difficult to implement in a public cloud with multiple data centers in different locations.
Lack of Control
Moving to the cloud means banks delegate physical control over their IT infrastructures. This may raise concerns about the ability to quickly respond to technical issues, configure solutions, or physically protect data. Dependence on a vendor can leave you vulnerable to downtime, service interruptions, or contract disputes. Also, cloud services for banks often take a one-size-fits-all approach, limiting the customization of applications or infrastructure.
Risk Management in Cloud Banking Systems
Let’s examine, how specific risks are managed in the context of cloud computing in banking and financial services.
Regulatory Compliance
Banks must first identify the regulatory requirements for their cloud operations, including data protection laws, financial regulations, and industry standards. Assess the cloud service provider’s compliance with all of them. Banks can mitigate regulatory risk by partnering with vendors with robust compliance programs and certifications like SOC 2, ISO 27001, etc.
Reputational Risk
To reduce the reputational risk of cloud incidents, it is essential to implement strong security measures, data protection practices, and disaster recovery plans. Also, create clear communication plans for transparent and quick resolution of incidents. Continuous monitoring of the cloud environment for threats and vulnerabilities is critical.
Operational Risk
Operational risks relate to the availability of services, data integrity, and the efficiency of cloud-based processes. To mitigate them, banks are implementing redundancy and disaster recovery mechanisms, backup solutions, and business continuity plans. Test these measures regularly to make sure they are working.
Strategic Risks
The implementation of cloud technology must be aligned with your business strategy. Consider factors like vendor lock-in, scalability, and cost-effectiveness. To mitigate risk, carefully select suppliers with flexible contractual arrangements and plan the adaption to changing market conditions and technology trends.
Final Thoughts
The importance of cloud services for banks is truly significant. This way of storing data is really popular nowadays, as traditional ways do not always manage to keep all the information. It’s really convenient to have one source for all the necessary data, and it definitely provides you with safety and accessibility. With the help of cloud services, you can also save costs and boost your productivity.
It’s easy to see that cloud computing is a must in today’s world, where everything is digitized. Though some companies still prefer old ways of managing information, to be compatible with the market you have to change your perspective and expand your experience. It’s essential to be open to new technologies, as the world is evolving. You can be sure that as time passes there will be more and more technologies to ease your life and help you achieve your goals with minimum challenges.
Inoxoft actively uses cloud computing in banking to develop clients’ bank products. Our priorities are security and compliance, automation of all the business processes, bringing innovations, and creating customer-central services. All these things are also benefits of cloud computing in banking. Inoxoft is constantly trying to keep up with the latest technologies to meet clients’ business demands. That’s why cloud computing is really important to our company.
Consider Inoxoft Your Trusted Partner
If you are looking for a reliable partner in banking software development, Inoxoft is exactly what you need. You can rely on us if you want to scale up your business. We provide automated services, security, and the best customer support. Our company constantly comes up with innovative ideas and solutions, as we try to keep up with all the latest developments. We will help you implement all the modern features, personalize your experience, and reduce possible risks you might face.
Inoxoft provides fintech software development services and banking software development services. Also, we will tell you everything you need to know if you are looking for information on the benefits of cloud services for banks. Our company uses best practices of project management and chooses a deliberate approach for each of our clients.
Inoxoft is the ultimate choice for anyone who is inspired to start or develop their own business and find a trusted partner. If you choose our company, we will not only ensure full transparency and accountability but also offer the best developer expertise. Contact us and learn everything you need to know about cloud adoption in banking services!
Frequently Asked Questions
What are the main reasons for cloud adoption in banking services?
There are many reasons why banks are cloud computing. They do it to boost their productivity, save costs and lower different potential risks. Scroll up if you want to know more about all these factors!
What is the importance of cloud computing in banking?
Cloud computing in the finance industry is quite important because it is convenient and up-to-date. Moreover, it's a great alternative to traditional ways of storing information.
Are cloud-based services reliable?
You can really count on cloud-based solutions, as they are able to store much more information that traditional storages. Read the article, if you are interested in other benefits of cloud computing in financial services!